February 18, 2026
The “Invisible” Revolution: Why Your Network’s Open Ports Are the New Phishing
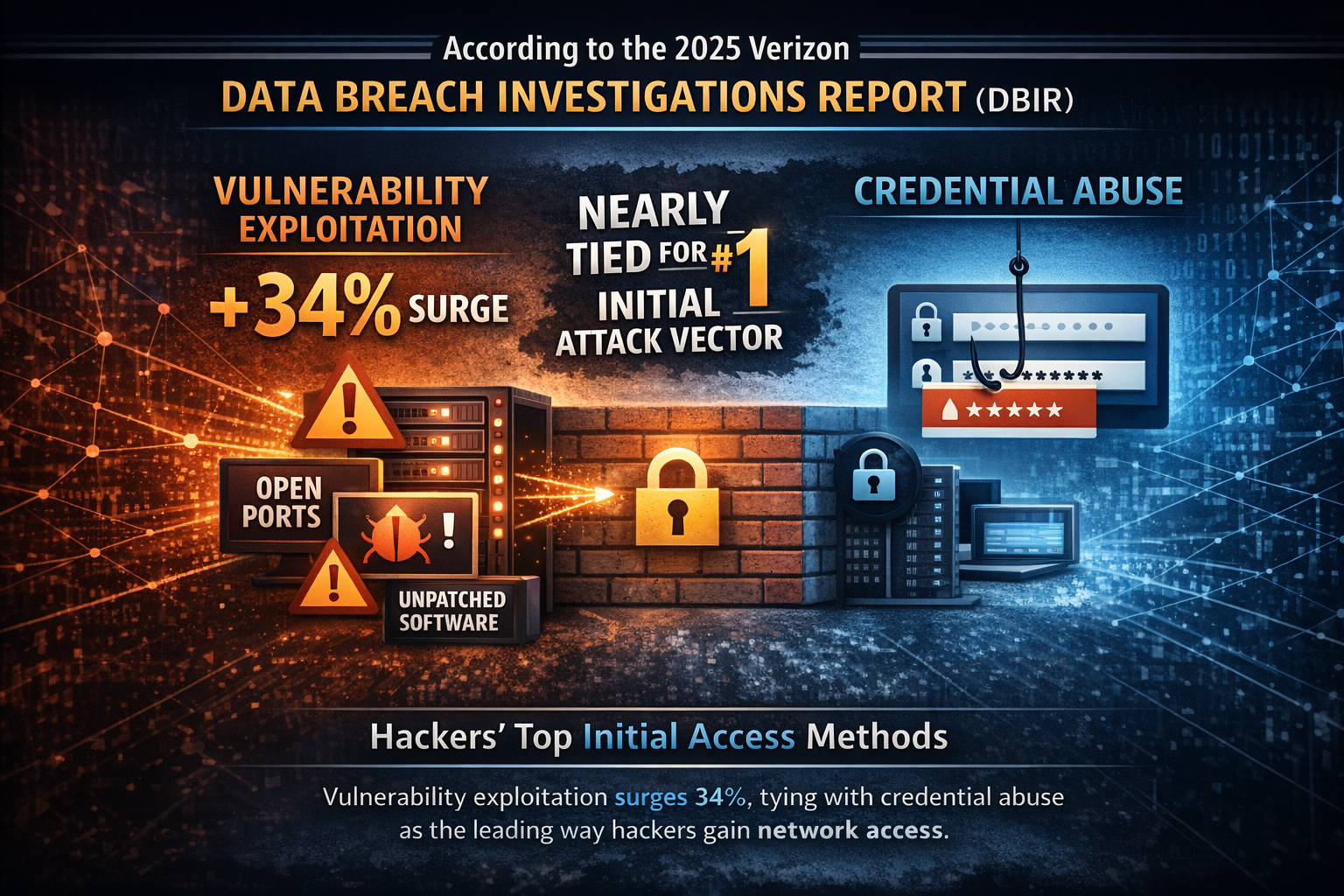
According to the 2025 Verizon Data Breach Investigations Report (DBIR), vulnerability exploitation—the act of targeting unpatched software and open network ports—has surged by 34%....

November 19, 2025
The Silent Threat: Why America’s Critical Infrastructure is Under Attack
As the attack surface expands—from industrial control networks to cloud-connected IoT sensors—traditional perimeter defenses no longer suffice. Security teams must assume compromise and reduce exposure...

July 15, 2025
The Hidden Vulnerability in Your IT Infrastructure: Why Open Ports Are Your Biggest Security Risk
By addressing the open port visibility problem, SSHepherd® helps organizations eliminate what many security experts consider the number one mistake leading to successful breaches. When...
June 3, 2025
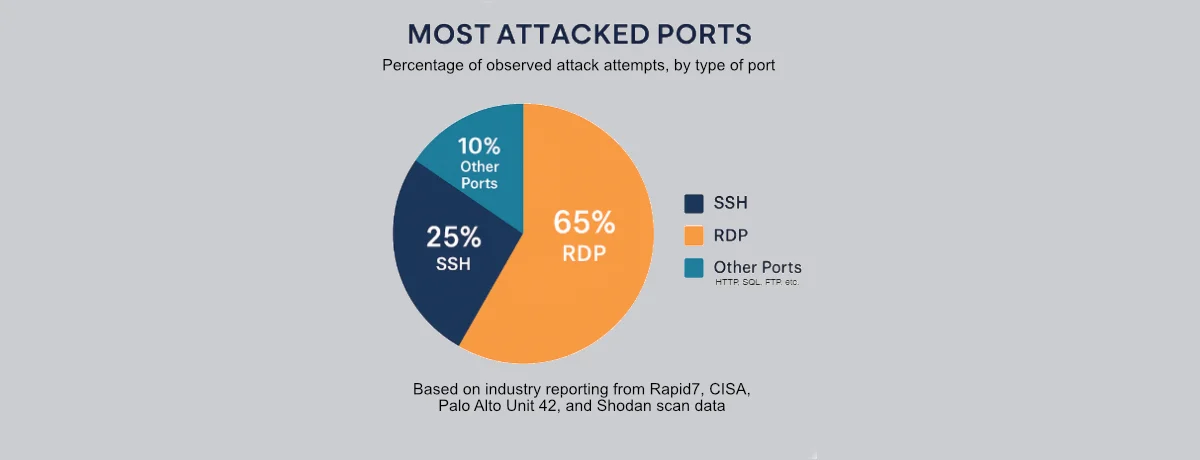
The 2 Most Dangerous and Attacked Ports in Your Environment
Industry reports consistently identify RDP and SSH as the most frequently attacked ports on the internet. Recent Shodan scans reveal the staggering scope of this...

April 9, 2025
Make Your Network Traffic Invisible to Hackers with SSHepherd
Traditional security measures like firewalls and encryption play a critical role, but they aren’t enough. If a hacker can see your ports, they can target...

April 9, 2025
How to Make MySQL Databases Invisible to Hackers with SSHepherd
When it comes to securing MySQL databases, most organizations are focused on encryption, firewalls, and authentication layers. But there’s one glaring risk that’s often overlooked:...

March 14, 2025
Making Your Websites Invisible to Hackers, Bots, and AI
As cybersecurity threats become more sophisticated, businesses of all sizes face an ongoing challenge: how do you keep sensitive websites and internal applications secure from...

January 15, 2025
How SSHepherd® Locks Down SSH Ports and Reduces Cybersecurity Risks
Cybersecurity professionals face an ongoing challenge: balancing the accessibility of network systems with the need to minimize vulnerabilities. Open SSH ports, critical for managing servers...

December 11, 2024
Invisible Fortresses: Securing Microsoft IIS Servers with SSHepherd
Microsoft Internet Information Services (IIS) powers countless critical web applications, from e-commerce platforms to internal business tools. As one of the most widely used web...

November 14, 2024
Invisible Fortresses: How SSHepherd Revolutionizes SFTP Server Security
In today’s digital landscape, the security of file transfers is paramount for organizations across all industries. Many businesses rely on SSH File Transfer Protocol (SFTP)...

August 30, 2024
Introduction to Linux Security Risks
Linux serves as the backbone behind most of the internet. Its widespread use makes it a prime target for hackers aiming to exploit vulnerabilities....
August 14, 2024
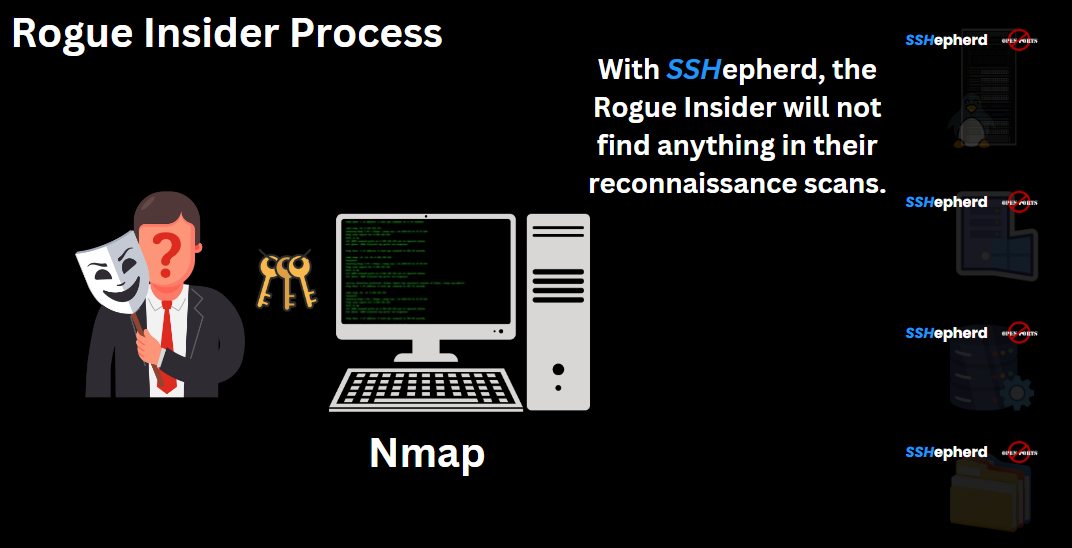
Understanding Insider Threats and How to Stop Them with SSHepherd
Insider threats pose one of the most challenging security risks for organizations today. Unlike external attacks, insider threats come from within the organization, making them...

July 26, 2024
Enhancing Cybersecurity with SSHepherd: A Comprehensive Mapping to NIST 800-53 Controls
SSHepherd, a powerful cybersecurity product, offers a range of features that map directly to multiple control families within NIST 800-53, enabling organizations to strengthen their...
July 14, 2024
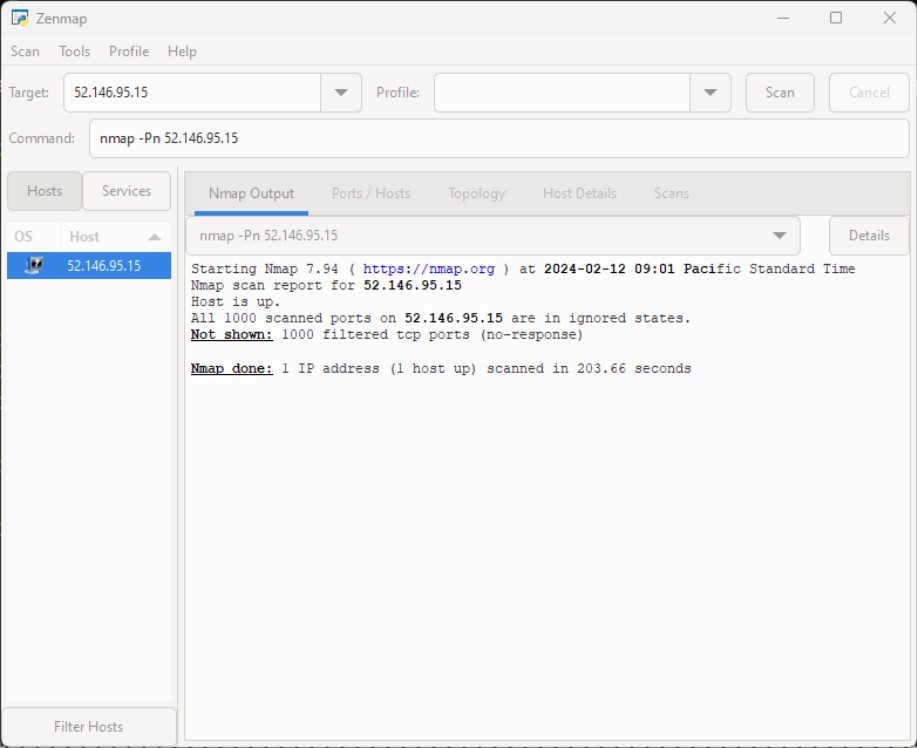
How to Make Your Windows RDP Environment Invisible to Hackers
In today’s world, securing your Remote Desktop Protocol (RDP) environment is crucial. Hackers constantly scan for open ports to exploit, and RDP servers are often...

June 25, 2024
The MITRE ATT&CK Framework and SSHepherd®
SSHepherd provides robust defense across the entire MITRE ATT&CK Framework by closing the very ports that attackers rely on throughout their exploits....

June 12, 2024
Securing Your Network by Identifying and Mitigating Open Ports
Understanding the open port attack surface is crucial for securing your network. In this blog, we’ll explore a couple of tools to help you identify...

May 28, 2024
Contain Phishing Exploits and Stop Ransomware Attacks
In today’s digital age, cybersecurity is under constant threat. The ability to contain a phishing exploit and stop a ransomware attack in its tracks is...
