February 18, 2026
The “Invisible” Revolution: Why Your Network’s Open Ports Are the New Phishing
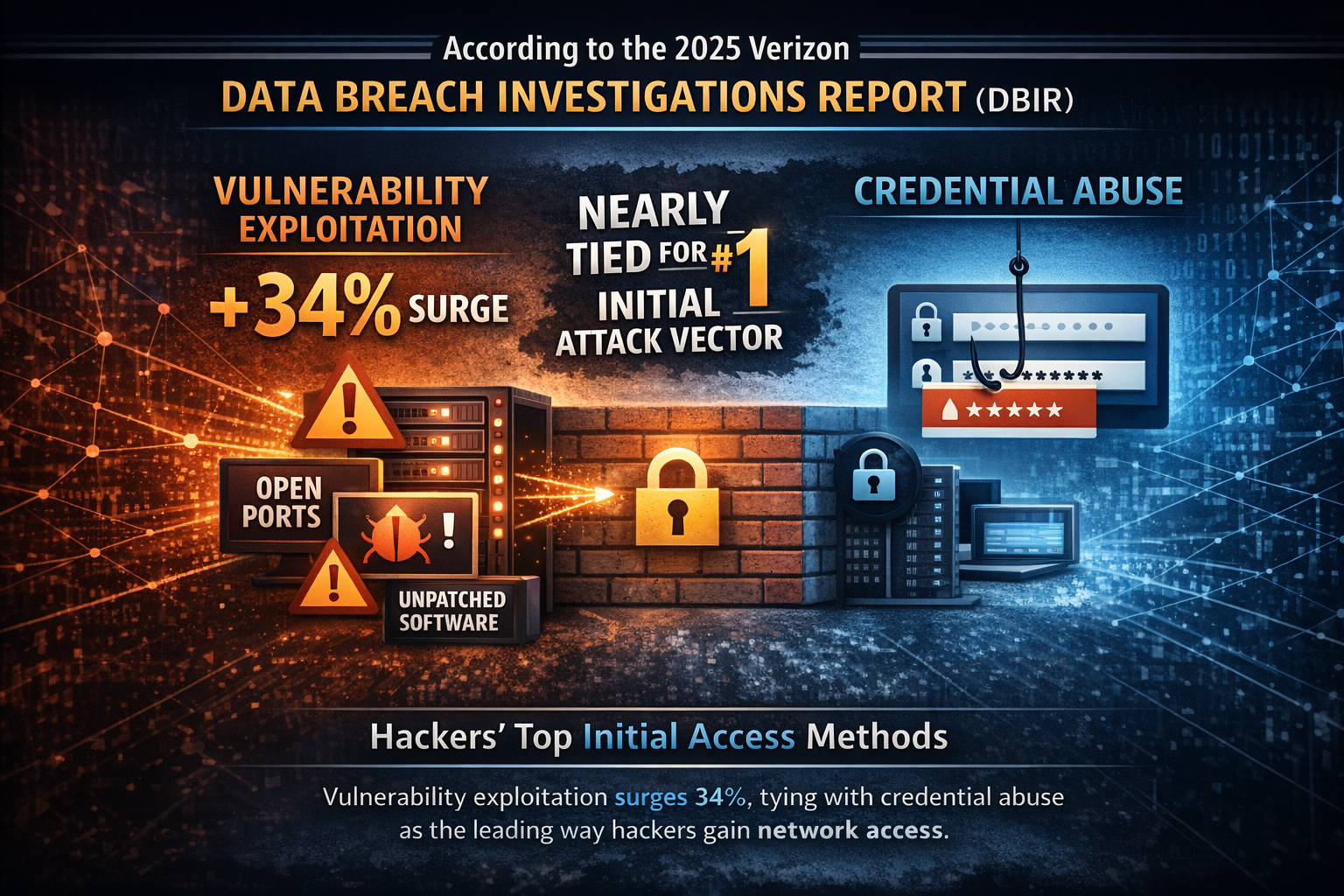
According to the 2025 Verizon Data Breach Investigations Report (DBIR), vulnerability exploitation—the act of targeting unpatched software and open network ports—has surged by 34%....

January 15, 2026
Implementing Zero Trust in Active Directory Through GPO Change Management
Platforms like UPA extend secure change control beyond traditional Windows domains to hybrid, cloud, and even non-domain-joined systems, helping you maintain consistent governance as your...

November 19, 2025
The Silent Threat: Why America’s Critical Infrastructure is Under Attack
As the attack surface expands—from industrial control networks to cloud-connected IoT sensors—traditional perimeter defenses no longer suffice. Security teams must assume compromise and reduce exposure...

October 22, 2025
Evaluating Your Next Group Policy Management Solution: Key Considerations for Enterprise AD Administrators After AGPM
Microsoft’s Advanced Group Policy Management (AGPM) has been the cornerstone of Group Policy change control for more than a decade. It gave enterprise administrators versioning,...

September 17, 2025
Hacker Exploits and GPOs: The Unseen Attack Vector in Your Active Directory
Group Policy Objects (GPOs) are essential for managing a secure Active Directory (AD) environment. They are a powerful administrative tool used to deploy settings, enforce...
August 19, 2025
Time to Modernize Your Group Policy Management
This blog dives into why MMC and GPMC fall short and how Full Armor’s Universal Policy Administrator (UPA) web-based platform revolutionizes GPO workflows....

July 15, 2025
The Hidden Vulnerability in Your IT Infrastructure: Why Open Ports Are Your Biggest Security Risk
By addressing the open port visibility problem, SSHepherd® helps organizations eliminate what many security experts consider the number one mistake leading to successful breaches. When...
June 3, 2025
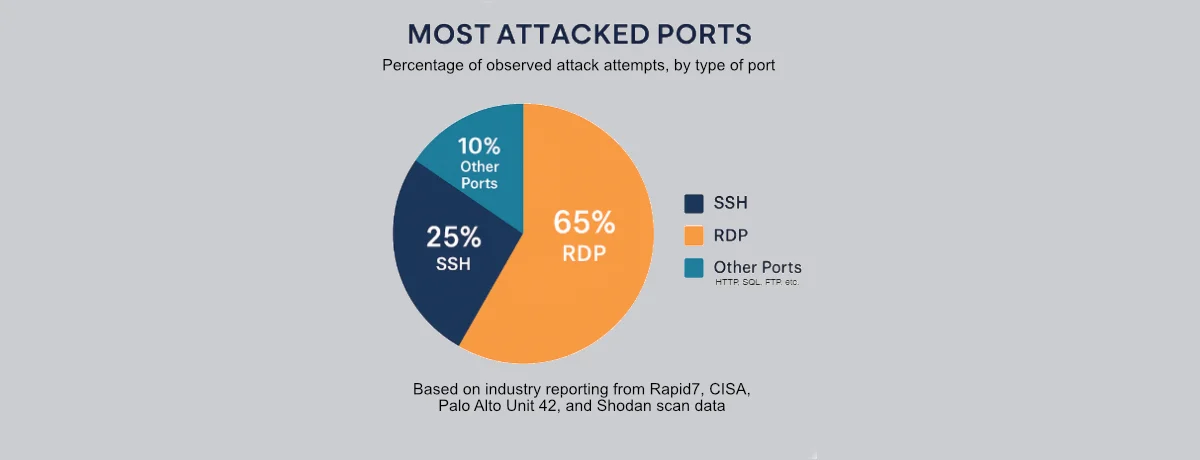
The 2 Most Dangerous and Attacked Ports in Your Environment
Industry reports consistently identify RDP and SSH as the most frequently attacked ports on the internet. Recent Shodan scans reveal the staggering scope of this...

March 14, 2025
Making Your Websites Invisible to Hackers, Bots, and AI
As cybersecurity threats become more sophisticated, businesses of all sizes face an ongoing challenge: how do you keep sensitive websites and internal applications secure from...

February 12, 2025
Revolutionize GPO Management: Preparing for AGPM’s End-of-Life and Beyond
As enterprises navigate the evolving landscape of IT infrastructure management, a significant milestone approaches that demands immediate attention: Microsoft’s Advanced Group Policy Management (AGPM) will...

January 15, 2025
How SSHepherd® Locks Down SSH Ports and Reduces Cybersecurity Risks
Cybersecurity professionals face an ongoing challenge: balancing the accessibility of network systems with the need to minimize vulnerabilities. Open SSH ports, critical for managing servers...
